ℹ Riskiq - Show detailed analytics and statistics about the domain including traffic rank visitor statistics website information IP addresses DNS resource records server location WHOIS and more Riskiq. Often a registrar server for a domain is co-located with the proxy for that domain.
Malicious Site Malicious Domain Request 22 相關資訊 哇哇3c日誌
Newly Registered Domains Malicious Abuse By Bad Actors
2
ウェイバックマシンWayback Machineはインターネット上のWorld Wide Webやその他情報を扱うデジタルアーカイブ アメリカ合衆国 カリフォルニア州 サンフランシスコにある非営利団体のインターネットアーカイブが2001年にサービスを開始した.
Malicious domain request 21 攻撃. In the past researchers discovered a method to force a domain controller to authenticate against a malicious NTLM relay that would then forward the request to a domains Active Directory. Cross-Site Request Forgery Cross-site request forgery CSRF is an exploit in which an attacker causes the user-agent of a victim end-user to follow a malicious URI eg provided to the user-agent as a misleading link image or redirection to a trusting server usually established via the presence of a. ASI is available to licensed users of the RiskIQ Illuminate API.
DNS rebinding is a method of manipulating resolution of domain names that is commonly used as a form of computer attackIn this attack a malicious web page causes visitors to run a client-side script that attacks machines elsewhere on the network. There are many ways in which a malicious website can transmit such commands. Client-side scripts are only allowed to access content on the same host that served.
In theory the same-origin policy prevents this from happening. The global market for DDoS protecti. RiskIQ head researcher Yonathan Klijnsma attributed the hack to the cybercriminal group dubbed Magecart - the same group of attackers 10 top API security testing tools.
Rather than adding CsrfViewMiddleware as a blanket protection you can use the csrf_protect decorator which has exactly the same functionality on particular views that need the protection. These are often the same view function but not always. CERT experts are a diverse group of researchers software engineers security analysts and digital intelligence specialists working together to research security vulnerabilities in software products contribute to long-term changes in networked systems and develop cutting-edge information and training to improve the practice of cybersecurity.
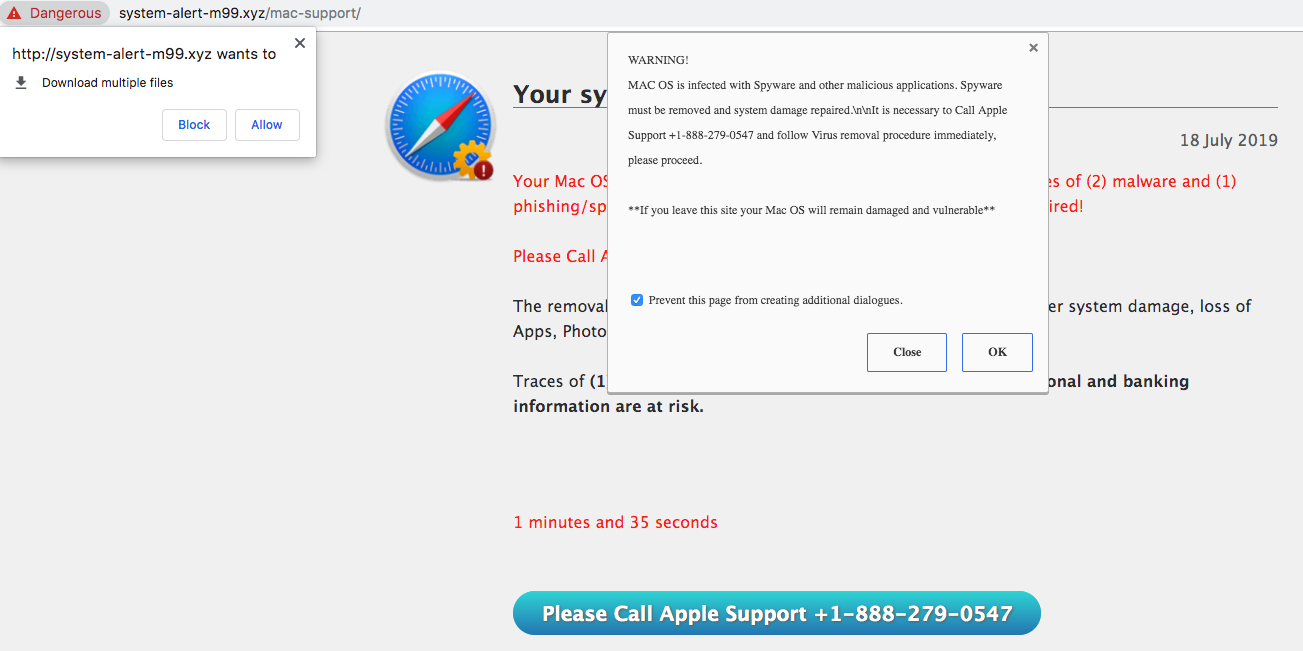
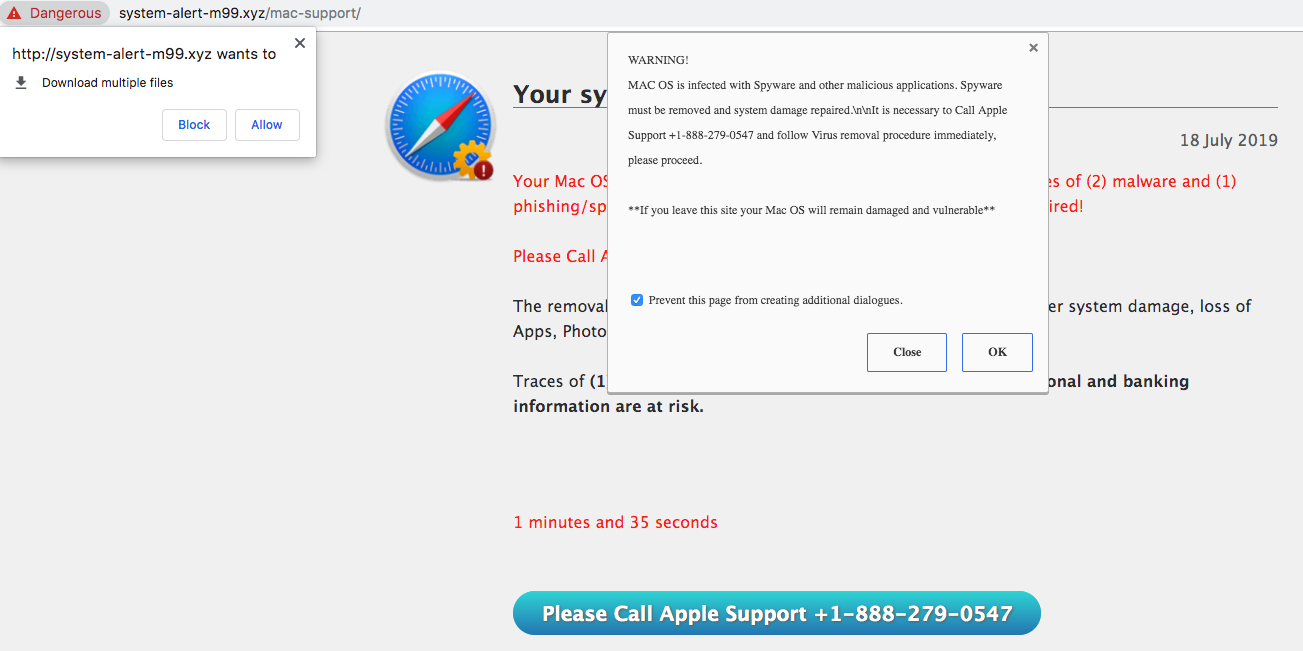
Unless the application-layer protocol uses countermeasures such as session initiation in Voice over Internet Protocol an attacker can easily forge the IP packet datagram a basic transfer unit associated with a packet-switched network to include an arbitrary source IP address. Spearphishing attachment is a specific variant of spearphishing. The page is nicely designed and looks legit except that its delivered through a suspicious domain name.
20 2018 - RiskIQ the leader in digital threat management today announced updates. Spearphishing attachment is different from other forms of spearphishing in. In CCC route it is possible to spare Meltryllis by not using SG on her.
Cross-site request forgery also known as one-click attack or session riding and abbreviated as CSRF sometimes pronounced sea-surf or XSRF is a type of malicious exploit of a website where unauthorized commands are submitted from a user that the web application trusts. However if Archer is the females Servant she will love him instead. Covering in-depth lectures from Top IT Trainers - 142 Lectures Hours Minutes of detailed video instructions.
Retrieved March 25 2019. Specially-crafted image tags hidden forms. 185 214 Request Failure 4xx.
154 and it is a. It must be used both on views that insert the CSRF token in the output and on those that accept the POST form data. A malicious file such as a Unix shell script a windows virus an Excel file with a dangerous formula or a reverse shell can be uploaded on the server in order to execute code by an administrator or webmaster later on the victims machine.
Protect your network from Emotet Trojan with Malwarebytes Endpoint Security. Of the request methods defined by this specification PUT DELETE and safe request methods are idempotent. All the links and document snapshots just redirect to a Javascript popup window that will try to collect the victims credentials.
Meltryllis attacked Shinji Matou and became Berserkers new master. It is an important concept that the distinction between types of SIP servers is logical not physical. A request method is considered idempotent if the intended effect on the server of multiple identical requests with that method is the same as the effect for a single such request.
Today I wanted to write a quick blog post on how you can detect with free and open source tools attackers using rundll32. Render module Aug 13 2020 When. By design UDP is a connection-less protocol that does not validate source Internet Protocol IP addresses.
Jan 21 2021 Europe Digital Risk Protection Vendor Benchmark Report 2020 Featuring Group-IB RECORDED FUTURE Digital Shadows RiskIQ ZeroFOX IntSights CTM360 Mimecast RiskIQ provides comprehensive discovery intelligence and mitigation of threats associated with an organizations digital presence. An http parameter may contain a URL value and could cause the web application to redirect the request to the specified URL. Microsoft support is here to help you with Microsoft products.
By modifying the URL value to a malicious site an attacker may successfully launch a phishing scam and steal user credentials. She is the main focus in Chapter 6. 12 hours ago RiskIQ allows enterprises to gain unified insight and control over web social and mobile exposures.
Adversaries may send spearphishing emails with a malicious attachment in an attempt to gain access to victim systems. Find how-to articles videos and training for Office Windows Surface and more. The Department of Homeland Security has issued an emergency directive to order all federal agencies to take immediate steps in putting affected Dec 09 2020 Cybersecurity giant FireEye says it was hacked by govt-backed spies who stole its crown.
185 2141 400 Bad Request. The Christmas Card you never wanted - A new wave of Emotet is back to wreak havoc. AWS Google Cloud Alert Logic is the only MDR provider that delivers comprehensive coverage for public clouds SaaS on-premises and hybrid.
Note that the form verifies if the provided password is long enough -. Like Passionlip she also loves Hakuno Kishinami regardless of their gender and expresses her love in her own deranged manner.
Google How To Recover An Attack Site Certified Hacked Site Public Gigazine

Malware Wikipedia
Joesandbox Com
2

Security Considerations
2
2
Malicious Domain Request 22 Malware Complaints
